Cloud computing is becoming increasingly popular amongst all kinds of businesses. 24/7 uptime, virtual machines leading to limited hardware, scalability, and reliability are just a few of the benefits of cloud computing over traditional computing techniques. There are 3 cloud service providers that dominate the market today, Amazon Web Service(AWS) Inc., Google, and Microsoft. However, for the past 10 years, AWS is ranked number one in Gartner’s Magic Quadrant as the top IaaS provider.
According to Amazon, there are over 1,000,000 active AWS users and it is ever-growing. Interestingly enough, the majority of AWS users are small or medium-sized business owners. AWS is a great cloud service provider that gives due importance to security. It is PCI Level 1 compliant. This is the highest compliance level and is only attained through a Qualified Security Assessor(QSA). AWS provides security tools that provide better overall security compared to traditional data centers.
However, there are some security issues to be mindful of. Some of them are overly permissive S3 bucket permissions and failure to enable logging on all S3 buckets. To avoid any cyberattacks or data leak, users have to do their bit as well. As an AWS user, it is important to conduct an AWS security audit from time to time. This article will help you understand what this security audit entails.
What Is AWS Security Audit
An AWS security is conducted to ensure the security configuration is set up correctly. Specifically, one should ensure that only authorized people have access, only the required permissions are given, and so on.
When To Conduct An AWS Security Audit
- Periodically! It is very important to include the audit as a regular security practice.
- Conduct a security audit when someone leaves the organization. Removing their access to AWS is important.
- While discontinuing any AWS service or removing/adding any software, conduct an audit and review permissions. Remove any unwanted permissions from users.
- If any suspicious activities are brought to your attention, conduct an audit. It is better to be safe than sorry.
How To Conduct An AWS Security Audit
To conduct an AWS security audit, follow the steps provided below. While auditing, make sure you are thorough. If there is anything in the configuration that doesn’t make sense to you, don’t let it slide. Read up about it or seek advice from security experts.
1) Review AWS Account Credentials
Remove the root access keys if it is not put to use. AWS itself recommends against root access keys unless you use AWS on a daily basis. If that’s the case, we highly recommend changing the keys periodically. Don’t forget to update all the applications and tools after this. The simplest way to change the access key:
- Open the IAM console after signing in
- Select Users>Security Credentials>Create access key> Download .csv file
- Store the newly generated access code.
- Check the last used column to identify whether the old access keys id still out to use. You can choose make inactive to resolve that issue.
Instead of root access keys, create IAM (Identity and Access Management) users. An IAM user is an entity capable of interacting with AWS. It represents a person or an application.
2) Review IAM Users
- Remove users that are inactive from the list of IAM users. Generate a credential report with all the IAM users, their AWS credentials like passwords and access keys.
- Review IAM groups and remove unwanted users from each group. You can create IAM groups when multiple IAM users have the same permissions.
3) Review IAM Roles
According to AWS, an IAM role is an IAM entity that defines a set of permissions for making AWS service requests. Similar to the previously discussed entities, review permissions of IAM roles and remove unwanted users.
4) Review Amazon EC2 Security Configuration
Amazon Elastic Compute Cloud or Amazon EC2 is a virtual server. Also known as compute instances, virtual servers are so much more convenient when compared to physical servers. It is scalable, resizable, quick, and inexpensive.
While conducting an audit, you also need to check the Amazon EC2 configurations for security loopholes. Identify any unused or unauthorized Amazon EC2 key pairs and delete them. Moreover, you also have to review the Amazon EC2 security groups. Inspect the permissions of the ports, protocols, and IP address ranges.
5) Review Mobile Apps That Requests To AWS
- Get temporary credentials on the app. You can do so by using APIs. This will help you authenticate users to the app. If this does not work, create a proxy server that dispenses temporary credentials to the app.
- Ensure the app does not have embedded access keys.
Benefits Of Having An AWS Security Audit
You can definitely follow these security practices and secure your AWS. However, this seems like a tedious task. Moreover, you will have to do this periodically. This is why it is better to get an AWS security audit instead of performing one on your own. Security audits provided by experts are tremendously effective. It will be much more comprehensive and hassle-free for you. Astra’s AWS Security Audit is exactly what you need to secure your AWS.
Conclusion
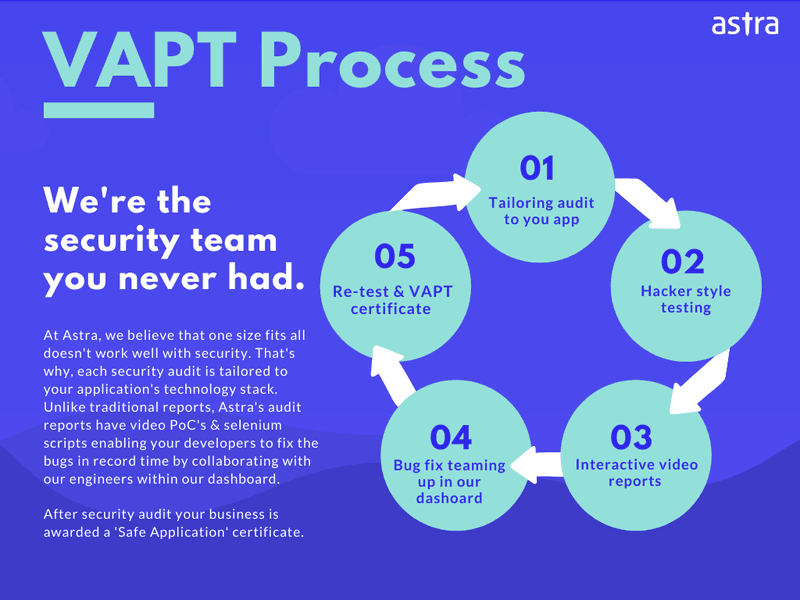
AWS is a popular IaaS that many companies use. However, it is important to carry out routine security practices to ensure the smooth running of your business. You can manually audit the security configuration of your AWS. For those looking to optimize their AWS infrastructure, aws serverless consulting can provide specialized guidance, ensuring that your cloud services are both secure and efficient. However, I’d say some things are best left to the experts. You can get AWS security from experts which are very efficient. Astra’s VAPT program is notably one of the best you’ll encounter.
Astra is a cybersecurity company that specializes in protecting websites and infrastructure. Under the Vulnerability Assessment and Penetration Test (VAPT) program, Astra provides an AWS security audit. The VAPT program follows all the major standards like OWASP, SANS, CERT, PCI, etc to identify open vulnerabilities in your AWS infrastructure.

Andrej Fedek is the creator and the one-person owner of two blogs: InterCool Studio and CareersMomentum. As an experienced marketer, he is driven by turning leads into customers with White Hat SEO techniques. Besides being a boss, he is a real team player with a great sense of equality.
